- Smart Tactics to Reduce Cloud Waste at Your Business
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste.
Cloud waste is the unnecessary spending of resources and money on cloud services. These services are often not fully utilized or optimized. About 32% of cloud spending is wasted. This can lead to budget concerns as spending
skyrockets.But that figure also holds opportunity. It means that you can reduce nearly a third of cloud spending by optimizing how you use cloud tools.
So, how can you reduce cloud waste at your business and save money? Here are some smart tactics to consider.
Conduct a Comprehensive Cloud Audit
Before implementing any cost-cutting strategies, conduct an audit. It’s essential to have a clear understanding of your current cloud usage. Conducting a comprehensive cloud audit allows you to identify:
- Underutilized resources
- Overprovisioned instances
- Unnecessary services
Use cloud management tools to generate reports. Look at usage patterns, costs, and performance metrics. This initial assessment forms the foundation for implementing effective waste reduction tactics.
Put in Place Right-Sizing Strategies
Right-sizing involves matching your cloud resources to the actual demands of your workloads. Many businesses fall into the trap of overprovisioning. This means securing more user licenses or features than they need. This leads to increased costs and unnecessary waste.
Analyze your workload requirements and resize instances accordingly. Use tools provided by your cloud service provider. These tools can identify and adjust the capacity of instances. This ensures that you only pay for the resources you truly need.
Use Reserved Instances and Savings Plans
Cloud providers offer cost-saving options like Reserved Instances (RIs) and Savings Plans. These allow businesses to commit to a specific amount of usage. This is in exchange for discounted rates. By leveraging these options, you can significantly reduce your cloud costs over time.
Carefully analyze your workload and usage patterns. Then, determine the most cost-effective reserved capacity or savings plan. Find a plan that aligns with your business’s long-term goals.
Install Automated Scaling Policies
Dynamic workloads have a need for dynamic resource allocation. Install automated scaling policies. These ensure that your infrastructure scales up or down based on demand. This optimizes performance. It also prevents overprovisioning during periods of low activity.
Cloud services enable you to set predefined policies for scaling. Examples are AWS Auto Scaling and Autoscale in Azure. These features help ensure efficient resource utilization without manual intervention.
Track and Optimize Storage
Storage costs can accumulate quickly. This is especially true when data is not regularly reviewed and archived. Estimate your storage needs. Then, put in place lifecycle policies to automatically downsize lesser-used data such as transitioning less frequently accessed data to lower-cost storage options.
Regularly review and delete unnecessary data to free up storage space. Adopt a proactive approach to storage management. This can help you significantly reduce costs associated with data storage.
Schedule Your Cloud Resources
Schedule your cloud resources to run only when you need them. For example, turn off development, testing, or staging environments during nights and weekends. Or scale down your production environment during off-peak hours.
Use available tools to automate the scheduling of your cloud resources. Base this on automated rules and policies that you define.
Delete Unused or Orphaned Cloud Resources
Sometimes, you may forget or neglect to delete cloud resources. Resources that you no longer need or use. This can include:
- Snapshots
- Backups
- Volumes
- Load balancers
- IP addresses
- Unused accounts
These resources can accumulate over time and incur unnecessary costs. To avoid this, you should regularly audit your cloud environment. Delete any unused or orphaned resources your business is not using. You can often use cloud provider tools to find and remove these.
Weed Out Duplicate Services
Different departments in the same organization may be using duplicate services. Marketing may use one task management app, while Sales uses a different one. Centralize cloud resources and remove duplicate tools.
Having everyone use the same cloud tool for the same function can save money as well as enhance collaboration, reporting, and data integration.
Embrace Serverless Architecture
Serverless computing allows businesses to run applications without managing the underlying infrastructure. You pay only for the actual compute resources used for your processes. This eliminates the need for provisioning and maintaining servers. Which reduces both operational complexity and costs. Consider migrating suitable workloads to a serverless model. This can help you optimize resource use and cut cloud waste.
Schedule a Cloud Optimization Assessment Today!
By following these smart tactics, you can reduce cloud waste at your business as well as optimize your cloud spending. This helps you save money. You can also improve operational efficiency and environmental sustainability.
Are you struggling with expanding cloud costs? Need help identifying and removing cloud waste? Our team of cloud experts can help you.
Contact us today to schedule your assessment.
This Article has been Republished with Permission from The Technology Press.
- Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world.
Often, it’s our own actions that leave us most at risk of a cyberattack or online scam. Risky behaviors include weak passwords and lax security policies. As well as thinking “This won’t happen to me.” This is why human error is the cause of approximately 88% of data breaches.
The National Cybersecurity Alliance and CybSafe are working to correct poor cyber hygiene. Each year, the duo publishes a report on cybersecurity attitudes and behaviors. The goal is to educate both people and businesses. To educate them on how to better secure their digital landscapes.
This year’s study surveyed over 6,000 people across the U.S., Canada, the U.K., Germany, France, and New Zealand. The survey asked about several things. These include knowledge of cybersecurity risks, security best practices, and challenges faced.
The report reveals some eye-opening insights. These include how people perceive and respond to cyber threats. As well as what they can do to improve their cybersecurity posture. Here are some of the key findings from the report.
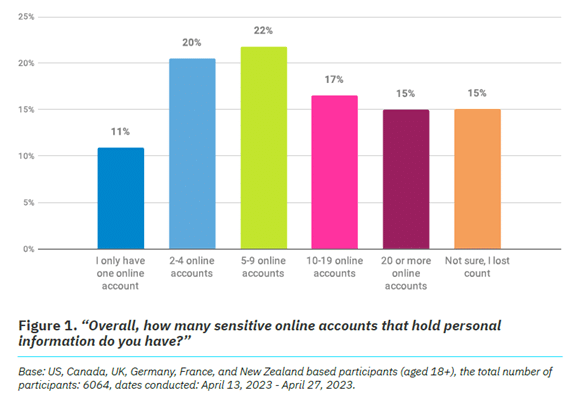
We Are Online… a Lot
It’s no surprise that 93% of the study participants are online daily. The logins we create continue to expand, as well as those considered “sensitive.” Sensitive accounts hold personal information that could be harmful if stolen.
Nearly half (47%) of the study’s respondents have ten or more sensitive online accounts. This amplifies risk. Especially if people are using the same password for two or more of those accounts.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 Online Security Makes People Frustrated
Most people (84%) feel that online security is a priority. But as many as 39% feel frustrated, and nearly the same amount intimidated. It can seem that you just can’t get ahead of the hackers. Just over half of people thought digital security was under their control. That leaves a whole lot that don’t think so.
But that is no reason to let down your defenses and become an easy target. There are best practices you can put in place to safeguard your online accounts that work.
These include:
- Enabling multi-factor authentication on your accounts
- Using an email spam filter to catch phishing emails
- Adding a DNS filter to block malicious websites
- Using strong password best practices
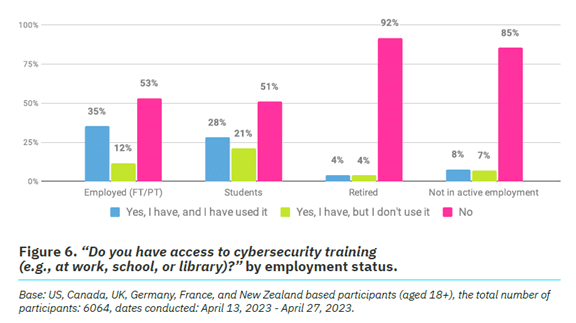
People Need More Access to Cybersecurity Training
One way to reduce human errors associated with cybersecurity is to train people. The survey found that just 26% of respondents had access to cybersecurity training.
It also broke this down by employment status. We see that those not actively employed are most lacking. Even those employed can use more training access and encouragement. Just 53% report having access to cybersecurity awareness training and using it.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 Employers can significantly reduce their risk of falling victim to a data breach. They can do this by beefing up their security awareness training. There is also a large opportunity to provide more training. Particularly to those retired or not actively employed.
Cybercrime Reporting Is Increasing
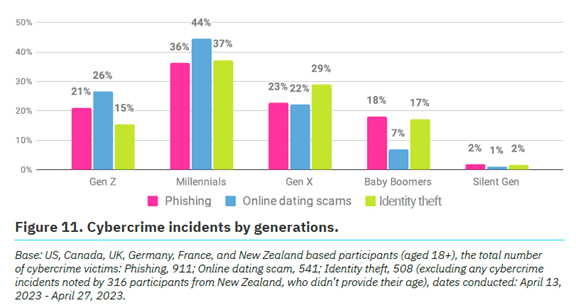
Over a quarter (27%) of survey participants said they had been a victim of cybercrime.
The types of cybercrimes reported include:
- Phishing (47%)
- Online dating scams (27%)
- Identity theft (26%)
Which generation reported the most cybercrime incidents? Millennials. In fact, Baby Boomers and the Silent Generation reported the fewest.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 No matter where you fall in the generations, it’s important to adopt security best
practices. We’ll go through some of these next.Online Security Best Practices to Reduce Your Risk
- Strong, Unique Passwords:
- Start with the basics. Create strong, unique passwords for each online account.
- Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Multi-Factor Authentication (MFA):
- Enhance your account security with multi-factor authentication.
- MFA adds an extra barrier to unauthorized access. Even for
compromised passwords.
- Regular Software Updates:
- Keep all your software, including operating systems and mobile
apps, up to date.
- Keep all your software, including operating systems and mobile
- Beware of Phishing Attacks:
- Exercise caution when clicking on links or opening attachments
especially in emails from unknown sources. - Verify the legitimacy of emails and websites. Check for subtle
signs, such as misspelled URLs or unfamiliar sender addresses.
- Exercise caution when clicking on links or opening attachments
- Use Secure Wi-Fi Networks:
- Ensure you connect to a secure and password-protected Wi-Fi
network. - Avoid using public Wi-Fi for sensitive transactions. Unless using a virtual private network (VPN).
- Ensure you connect to a secure and password-protected Wi-Fi
- Data Backup:
- Regularly back up important data to an external device or a secure
cloud service.
- Regularly back up important data to an external device or a secure
- Use Antivirus and Anti-Malware Software:
- Install reputable antivirus and anti-malware software on all devices.
- Regularly scan your systems for potential threats.
- Be Mindful of Social Media Settings:
- Review and adjust your privacy settings on social media platforms.
- Limit the amount of personal information visible to the public.
- Secure Your Personal Devices:
- Lock your devices with strong passwords or biometric
authentication.
- Lock your devices with strong passwords or biometric
- Educate and Stay Informed:
- Educate yourself and your team through cybersecurity awareness
programs. This fosters a culture of vigilance and preparedness.
- Educate yourself and your team through cybersecurity awareness
Schedule Cybersecurity Awareness Training Today
A little education on cybersecurity goes a long way toward protecting your data. Our experts can provide security training at the level you need. We’ll help you fortify your defenses against phishing, scams, and cyberattacks.
Contact us today to schedule a chat.
This Article has been Republished with Permission from The Technology Press.
- Be Careful When Scanning QR Codes – There’s a New Scam Going Around!
QR codes are everywhere these days. You can find them on restaurant menus, flyers, and posters. They’re used both offline and online. QR codes are convenient and easy to use. You just scan them with your smartphone camera. You’re then directed to a link, a coupon, a video, or some other online content.
With the rise in popularity of QR codes comes an unfortunate dark side. Cybercriminals are exploiting this technology for nefarious purposes. Scammers create fake QR codes. They can steal your personal information. They can also infect your device with malware or trick you into paying money.
It’s crucial to exercise caution when scanning QR codes. This emerging scam highlights the potential dangers lurking behind those seemingly innocent squares.
Image source: Adobe Stock The QR Code Resurgence
QR codes were originally designed for tracking parts in the automotive industry. They have experienced a renaissance in recent years. As a result, they’re used as a form of marketing today.
They offer the convenience of instant access to information. You simply scan a code. They’ve become an integral part of various industries, including retail and hospitality.
Unfortunately, cybercriminals are quick to adapt. A new phishing scam has emerged, exploiting the trust we place in QR codes.
How the Scam Works
The scammer prints out a fake QR code. They place it over a legitimate one. For example, they might stick it on a poster that advertises a product discount or a movie.
You come along and scan the fake QR code, thinking it’s legitimate. The fake code may direct you to a phishing website. These sites may ask you to enter sensitive data. Such as your credit card details, login credentials, or other
personal information.Or scanning the QR code may prompt you to download a malicious app. One that contains malware that can do one or more of the following:
- Spy on your activity
- Access your copy/paste history
- Access your contacts
- Lock your device until you pay a ransom
The code could also direct you to a payment page. A page that charges you a fee for something supposedly free.
Here are some tactics to watch out for.
Malicious Codes Concealed
Cybercriminals tamper with legitimate QR codes. They often add a fake QR code sticker over a real one. They embed malicious content or redirect users to fraudulent websites.
Fake Promotions and Contests
Scammers often use QR codes to lure users into fake promotions or contests. When users scan the code, it may direct them to a counterfeit website. The website may prompt them to provide personal information. This can lead to potential identity theft or financial fraud.
Malware Distribution
Some malicious QR codes start downloads of malware onto the user’s device. This can result in compromised security. Including unauthorized access to personal data and potential damage to the device’s functionality.
Stay Vigilant: Tips for Safe QR Code Scanning
Verify the Source
Be cautious when scanning QR codes from unknown or untrusted sources. Verify the legitimacy of the code and its source. This is especially true if it prompts you to enter personal information.
Use a QR Code Scanner App
Consider using a dedicated QR code scanner app. Use that rather than the default camera app on your device. Some third-party apps provide extra security features. Such as code analysis and website reputation checks.
Inspect the URL Before Clicking
Before visiting a website prompted by a QR code, review the URL. Ensure it matches the legitimate website of the organization it claims to represent.
Avoid Scanning Suspicious Codes
Trust your instincts. If a QR code looks suspicious, refrain from scanning it. Scammers often rely on users’ curiosity. Be careful when scanning QR codes that you see in public places. Don’t scan them if they look suspicious, damaged, or tampered with. Exercising caution is paramount.
Update Your Device and Apps
Keep your device’s operating system and QR code scanning apps up to date. Regular updates often include security patches that protect against known vulnerabilities.
Be Wary of Websites Accessed via QR Code
Don’t enter any personal information on a website that you accessed through a QR code. This includes things like your address, credit card details, login information, etc.
Don’t pay any money or make any donations through a QR code. Only use trusted and secure payment methods.
Contact Us About Phishing Resistant Security Solutions
QR codes can be useful and fun. But they can also be dangerous if you’re not careful. Always scan them with caution. Protect yourself from scammers who want to take advantage of your curiosity.
This scam falls under the umbrella of phishing. Phishing is one of the most dangerous modern risks for individuals and organizations. If you need help ensuring your devices are phishing resistant, just let us know.
Contact us today to learn more.
This Article has been Republished with Permission from The Technology Press.
- 9 Signs That Your Smart Home Device Has Been Hacked
Smart home devices are becoming more popular and convenient. But they also pose some serious security risks. Hackers can target these devices to access your personal information. As well as spy on your activities or cause damage to your home.
Often the dangers of smart home devices fall under the radar. Seventy-five percent of people feel some level of distrust about the use of their data. Yet most people are willing to use smart home technology.
As we enjoy the convenience of smart living, it’s crucial to be vigilant about cyber threats. A hacker may have compromised your smart system without you even knowing it.
How can you tell if a hacker has compromised your smart home device? Here are some signs to look out for.
1. Unexpected Behavior
Unexpected behavior is the first sign someone has compromised your smart home device. If your device starts acting erratically, it’s time to investigate. Erratic behavior can include:
- Lights flickering
- Thermostat settings changing
- Smart locks behaving unpredictably
Hackers often manipulate smart devices to create disturbances. Noticing these irregularities early can prevent further damage.
2. Unusual Network Traffic
Monitoring your home network is a fundamental aspect of cybersecurity. Have you observed a sudden surge in data usage? Noticed unusual patterns in network traffic? If so, this could indicate unauthorized access.
Hackers may exploit your smart devices to launch attacks or steal sensitive information. Regularly check your router’s activity logs. This helps you stay vigilant against abnormal network behavior.
3. Strange Sounds or Voices
Smart speakers and voice-activated assistants have become commonplace in many households. If you start hearing unfamiliar voices or strange sounds from these devices, it’s a red flag.
Hackers may use compromised devices to eavesdrop or communicate with household members. This poses serious privacy concerns. Ensure that your smart devices are only responding to authorized voices.
4. Device Settings Modification
Smart devices offer customizable settings to cater to individual preferences. Have you noticed unauthorized changes to these settings? Such as alterations in camera angles, sensor sensitivity, or device preferences? If so, there’s a high likelihood that a hacker has compromised your device.
Regularly review and update your device settings. This helps you maintain control over your smart home ecosystem.
5. Unexplained Data Transfers
Smart devices often collect and send data to the cloud for analysis or storage. Keep an eye on your device’s data usage. Be wary of unexplained data transfers. Hackers may exploit vulnerabilities to extract sensitive information from your devices.
Regularly review the data usage patterns of your smart devices. This helps you to identify any suspicious activity.
6. Device Inaccessibility
Suddenly finding yourself locked out of your smart home devices could be a sign of hacking. Hackers may change passwords or enable two-factor authentication without your consent. They can take control of your accounts. This renders you unable to access or manage your devices.
Always act promptly to regain control. Secure your accounts if you suspect unauthorized access.
7. New or Unknown Devices on the Network
Regularly review the list of devices connected to your home network. Do you spot unfamiliar or unauthorized devices? If so, it’s a clear sign that someone may have breached your network.
Hackers often connect to your network. They do this to exploit vulnerabilities in smart devices or launch attacks. Secure your network with strong passwords. Also, consider implementing network segmentation for added protection.
8. Frequent Software Glitches
Smart devices receive regular software updates. These updates patch vulnerabilities and enhance security. Have you noticed frequent software glitches? Or has your device failed to update? It could be a sign of interference
by a malicious actor.Ensure that your smart devices are running the latest firmware. This ensures it has the latest security patches and bug fixes installed.
9. Emails or Messages Confirming Changes You Didn’t Make
Some smart devices send notifications or emails to confirm changes such as changes in settings, passwords, or device access. Did you receive such confirmations for actions you didn’t take? If so, this is a clear sign of unauthorized access.
Take immediate action to secure your account. This includes changing passwords and reviewing access permissions.
Need Help Securing Your Smart Home & Peace of Mind?
As our homes become smarter, so must our approach to cybersecurity. The first step in safeguarding your digital domain is recognizing signs. The signs that a hacker has compromised your smart home device.
Remember, smart home devices can make your life easier and more comfortable. But they also need careful maintenance and protection.
Need some guidance? We can help you ensure that your smart home remains a secure haven of innovation. Instead of a vulnerable target for cyber threats.
Contact us today to schedule a smart home security consultation.
This Article has been Republished with Permission from The Technology Press.
- 5 Cybersecurity Predictions for 2024 You Should Plan For
Cybersecurity is a constantly evolving field. There are new threats, technologies, and opportunities emerging every year. As we enter 2024, organizations need to be aware of current and future cyber threats. Businesses of all sizes and sectors should plan accordingly.
Staying ahead of the curve is paramount to safeguarding digital assets. Significant changes are coming to the cybersecurity landscape. Driving these changes are emerging technologies and evolving threats. As well as shifting
global dynamics.Next, we’ll explore key cybersecurity predictions for 2024 that you should consider.
1. AI Will Be a Double-edged Sword
Artificial intelligence (AI) has been a game-changer for cybersecurity. It has enabled faster and more accurate threat detection, response, and prevention. But AI also poses new risks. Such as adversarial AI, exploited vulnerabilities, and misinformation.
For example, malicious actors use chatbots and other large language models to generate:
- Convincing phishing emails
- Fake news articles
- Deepfake videos
This malicious content can deceive or manipulate users. Organizations will need to put in place robust security protocols. This includes embracing a human-in- the-loop approach. As well as regularly tracking and reviewing their AI systems. These steps will help them mitigate these risks and harness the power of AI for a more secure future.
2. Quantum Computing Will Become a Looming Threat
Quantum computing is still a few years away from reaching its full potential. But it is already a serious threat to the security of current encryption standards.
Quantum computers can potentially break asymmetric encryption algorithms. These algorithms are widely used to protect data in transit and at rest. This means that quantum-enabled hackers could compromise sensitive data, like financial transactions.
Organizations will need to start preparing for this scenario. They can do this by assessing their potential risks first. Then, adopting quantum-resistant technologies and deploying quantum-safe architectures.
3. Hacktivism Will Rise in Prominence
Hacktivism is the use of hacking techniques to promote a political or social cause such as exposing corruption, protesting injustice, or supporting a movement.
Hacktivism has been around for decades. But it’s expected to increase in 2024. Particularly during major global events. These may include the Paris Olympics and the U.S. Presidential Election as well as specific geopolitical conflicts.
Hacktivists may target organizations that they perceive as adversaries or opponents. This can include governments, corporations, or media outlets. These attacks can disrupt their operations. As well as leak their data or deface their websites.
Organizations will need to be vigilant against potential hacktivist attacks. This includes being proactive in defending their networks, systems, and reputation.
4. Ransomware Will Remain a Persistent Threat
Ransomware is a type of malware that encrypts the victim’s data. The attacker then demands a ransom for its decryption. Ransomware has been one of the most damaging types of cyberattacks in recent years.
In 2023, ransomware attacks increased by more than 95% over the prior year.
Ransomware attacks are likely to continue increasing in 2024. Due to new variants, tactics, and targets emerging. For example, ransomware attackers may leverage AI to enhance their encryption algorithms as well as evade detection and customize their ransom demands.
Hackers may also target cloud services, IoT devices, or industrial control systems. This could cause more disruption and damage. Organizations will need to put in place comprehensive ransomware prevention and response strategies. Including:
- Backing up their data regularly
- Patching their systems promptly
- Using reliable email and DNS filtering solutions
- Educating their users on how to avoid phishing emails
5. Cyber Insurance Will Become More Influential
Cyber insurance covers the losses and liabilities resulting from cyberattacks. It has become more popular and important in recent years. This is due to cyberattacks becoming more frequent and costly.
Cyber insurance can help organizations recover from cyber incidents faster and more effectively. It provides financial compensation, legal help, or technical support.
But cyber insurance can also influence the security practices of organizations. More cyber insurers may impose certain requirements or standards on their customers. Such as implementing specific security controls or frameworks. Organizations will need to balance the benefits and costs of cyber insurance as
well as ensure that they are in compliance with their cyber insurers’ expectations.Be Proactive About Cybersecurity – Schedule an Assessment
It’s clear that the cybersecurity landscape will continue to evolve rapidly. Organizations and individuals must proactively prepare for emerging threats. This includes adopting advanced technologies and prioritizing workforce development as well as staying abreast of regulatory changes.
Put a comprehensive cybersecurity strategy in place. One that encompasses these predictions. This will help you navigate the digital frontier with resilience and vigilance.
Need help ensuring a secure and trustworthy digital environment for years to come? Contact us today to schedule a cybersecurity assessment.
This Article has been Republished with Permission from The Technology Press.