- Beware of Deepfakes! Learn How to Spot the Different Types
Have you ever seen a video of your favorite celebrity saying something outrageous? Then later, you find out it was completely fabricated? Or perhaps you’ve received an urgent email seemingly from your boss. But something felt off.
Welcome to the world of deepfakes. This is a rapidly evolving technology that uses artificial intelligence (AI). It does this to create synthetic media, often in the form of videos or audio recordings. They can appear real but are actually manipulated.
People can use deepfakes for creative purposes. Such as satire or entertainment. But their potential for misuse is concerning. Deepfakes have already made it into political campaigns. In 2024, a fake robocall mimicked the voice of a candidate. Scammers wanted to fool people into believing they said something they never said.
Bad actors can use deepfakes to spread misinformation. As well as damage reputations and even manipulate financial markets. They are also used in phishing attacks. Knowing how to identify different types of deepfakes is crucial in today’s world.
So, what are the different types of deepfakes, and how can you spot them?
Face-Swapping Deepfakes
This is the most common type. Here the face of one person is seamlessly superimposed onto another’s body in a video. These can be quite convincing, especially with high-quality footage and sophisticated AI algorithms.
Here’s how to spot them:
- Look for inconsistencies: Pay close attention to lighting, skin tones, and facial expressions. Do they appear natural and consistent throughout the video? Look for subtle glitches. Such as hair not moving realistically. Or slight misalignments around the face and neck.
- Check the source: Where did you encounter the video? Was it on a reputable news site or a random social media page? Be cautious of unverified sources and unknown channels.
- Listen closely: Does the voice sound natural? Does it match the person’s typical speech patterns? Incongruences in voice tone, pitch, or accent can be giveaways.
Deepfake Audio
This type involves generating synthetic voice recordings. They mimic a specific person’s speech patterns and intonations. Scammers can use these to create fake audio messages. As well as make it seem like someone said something they didn’t.
Here’s how to spot them:
- Focus on the audio quality: Deepfake audio can sound slightly robotic or unnatural. This is especially true when compared to genuine recordings of the same person. Pay attention to unusual pauses. As well as inconsistent pronunciation or a strange emphasis.
- Compare the content: Does the content of the audio message align with what the person would say? Or within the context in which it’s presented? Consider if the content seems out of character or contradicts known facts.
- Seek verification: Is there any independent evidence to support the claims made? If not, approach it with healthy skepticism.
Text-Based Deepfakes
This is an emerging type of deepfake. It uses AI to generate written content. Such as social media posts, articles, or emails. They mimic the writing style of a specific person or publication. These can be particularly dangerous. Scammers can use these to spread misinformation or impersonate someone online.
Here’s how to spot them:
- Read critically: Pay attention to the writing style, vocabulary, and tone. Does it match the way the person or publication typically writes? Look for unusual phrasing, grammatical errors, or inconsistencies in tone.
- Check factual accuracy: Verify the information presented in the text against reliable sources. Don’t rely solely on the content itself for confirmation.
- Be wary of emotional triggers: Be cautious of content that evokes strong emotions. Such as fear, anger, or outrage. Scammers may be using these to manipulate your judgment.
Deepfake Videos with Object Manipulation
This type goes beyond faces and voices. It uses AI to manipulate objects within real video footage. Such as changing their appearance or behavior. Bad actors may be using this to fabricate events or alter visual evidence.
Here’s how to spot them:
- Observe physics and movement: Pay attention to how objects move in the video. Does their motion appear natural and consistent with the laws of physics? Look for unnatural movement patterns. As well as sudden changes in object size, or inconsistencies in lighting and shadows.
- Seek original footage: If possible, try to find the original source of the video footage. This can help you compare it to the manipulated version and identify alterations.
Staying vigilant and applying critical thinking are crucial in the age of deepfakes.
Familiarize yourself with the different types. Learn to recognize potential red flags. Verify information through reliable sources. These actions will help you become more informed and secure.
Get a Device Security Checkup
Criminals are using deepfakes for phishing. Just by clicking on one, you may have downloaded a virus. A device security checkup can give you peace of mind. We’ll take a look for any potential threats and remove them.
Contact us today to learn more.
This Article has been Republished with Permission from The Technology Press.
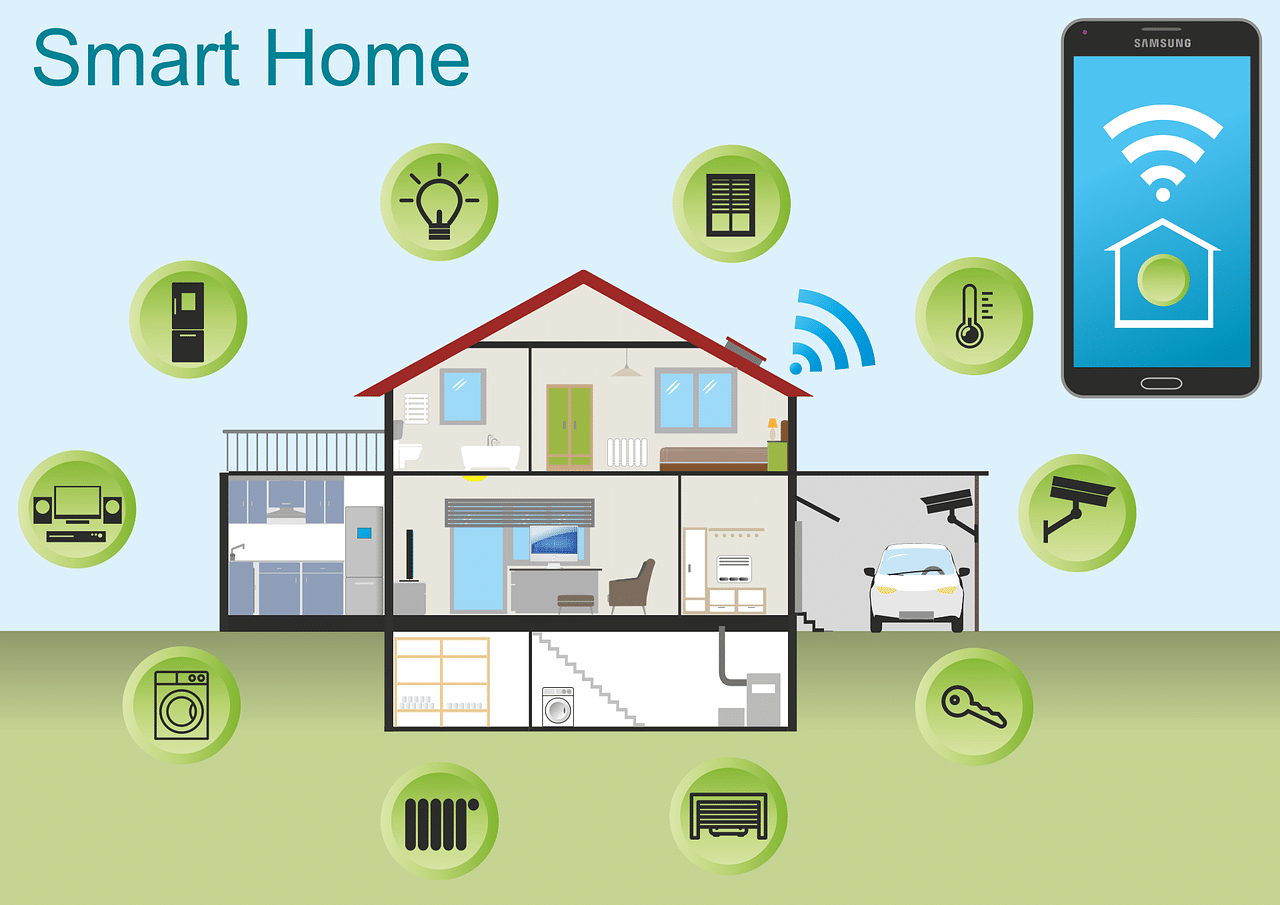
- 10 Most Common Smart Home Issues (and How to Fix Them)
Back when you were a kid, living in a “smart home” probably sounded futuristic. Something out of Back to the Future II or The Jetsons. Well, we don’t yet have flying cars, but we do have video telephones as well as smart refrigerators and voice-activated lights.
But even the most advanced technology can have analog problems. Hackers can get past weak passwords. Bad connections can turn advanced into basic pretty quickly.
Have you run into any issues with your smart home gadgets? Not to worry! We’ve got your back when it comes to troubleshooting several common smart home issues.
Here are some of the most frequent problems along with simple steps to get your smart haven back on track.
1. Connectivity Woes
Are your smart gadgets refusing to connect to Wi-Fi? The main claim to fame of smart devices is that you can access them wirelessly. An internet connection is also vital to integrate several devices into a smart home hub.
If your device is having connection issues, check the basics first. Restart your router and your devices. If that doesn’t work, ensure you’ve positioned your router centrally. This gives you optimal signal strength. Consider a mesh network for large houses. Or invest in a Wi-Fi extender for better coverage.
2. Device Unresponsiveness
Now that we have voice-activated devices, we expect them to always answer. It can be frustrating when a device won’t respond to its “wake word.” We might even raise our voice and ask again… only to be ignored.
Are you having trouble with your smart devices not responding to commands? A simple power cycle (turning them off and on) can often do the trick. Check for software updates on your devices. As well as the corresponding apps. Updating software can fix bugs and improve performance.
3. Battery Drain
Smart devices, especially those battery-powered, can drain quickly. Adjust settings to reduce power consumption. Disable features you don’t use. Such as notification lights or constant background updates. Consider replacing batteries with high-quality ones for optimal performance.
4. Incompatibility Issues
Not all smart devices are created equal. Just because it says “smart” on the box doesn’t mean it plays well with others. When a new device won’t interact with your network, it can mean money down the drain.
Before you buy, check to ensure your devices are compatible with each other. Build your devices around your smart home platform. Review the manufacturer’s specifications thoroughly to avoid compatibility headaches.
5. Security Concerns
Security is paramount in a smart home. There have been horror stories about hacked baby monitors. These stories can get real very fast. You need to pay attention to securing your devices. Rather than getting caught up in plugging them in as fast as possible.
Use strong and unique passwords for all your devices and accounts. Enable two-factor authentication wherever available. Keep your devices and apps updated with the latest security patches.
A few other smart device security tips include:
- Change the default device name on your network. Choose something generic.
- Put smart devices on a separate “guest” network. This keeps them separated from devices with more sensitive data.
- Turn off unnecessary sharing features. These are often enabled by default.
6. App Troubles
Are you running into sporadic problems? Bugs that crop up intermittently?
Sometimes, the problem might lie with the app itself. Check if any app updates are available and install them. Try logging out and logging back in to refresh the connection. If issues persist, uninstall and reinstall the app.
7. Automation Gone Wrong
Smart home automations can be convenient, but sometimes they malfunction. Review your automation rules and ensure they’re set up correctly. Test them individually to identify any faulty triggers or actions.
8. Limited Range
Some smart devices have a limited range. Check the manufacturer’s guide so you know what to expect. Move your devices closer to the hub or router for better communication. Consider using repeaters or extenders if the distance is an issue.
9. Ghost Activity
Ever experienced your smart lights turning on or off randomly? This could be due to factors such as:
- Accidental voice commands
- Faulty sensors
- Scheduled automations you forgot about
- A hacked device
Review your automation settings and disable any you don’t need. Investigate if your devices are picking up unintended voice commands from other sources. Change passwords and watch out for breaches.
10. Feeling Overwhelmed
It’s easy to get overwhelmed when you’re dealing with several smart devices. Don’t hesitate to consult your device manuals and online resources. You can also get help from our IT experts for specific troubleshooting steps. These resources can offer more guidance tailored to your situation.
Need Help Securing Your Smart Home?
A smart home should simplify your life, not complicate it. These simple solutions can help you navigate common issues. It’s also important to get a smart home security assessment to keep your family protected.
Contact us today to schedule a security checkup for your smart home and gain peace of mind.
This Article has been Republished with Permission from The Technology Press.
- What Is Microsoft Security Copilot? Should You Use It?
It can be challenging to keep up with the ever-evolving cyber threat landscape. Companies need to process large amounts of data. As well as respond to incidents quickly and effectively. Managing an organization’s security posture is complex.
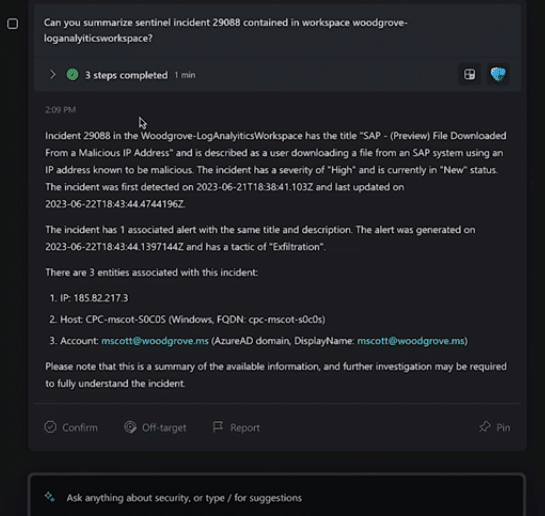
That’s where Microsoft Security Copilot comes in. Microsoft Security Copilot is a generative AI-powered security solution. It provides tailored insights that empower your team to defend your network. It works with other Microsoft security products. It also integrates with natural language to generate tailored guidance and insights.
In this article, we will explain what Microsoft Security Copilot is. We’ll explore its benefits and whether it’s the right choice to enhance your digital defenses.
What Is Microsoft Security Copilot?
Microsoft Security Copilot is a cutting-edge cybersecurity tool. It leverages the power of AI and machine learning for threat detection and response. Copilot aims to enhance the efficiency and effectiveness of cybersecurity operations.
Microsoft Security Copilot helps security teams:
- Respond to cyber threats
- Process signals
- Assess risk exposure at machine speed
It works with other Microsoft security products as well. A big benefit is that it integrates with natural language. This means you can ask questions plainly to generate tailored guidance and insights.
Security Copilot can help with end-to-end scenarios such as:
- Incident response
- Threat hunting
- Intelligence gathering
- Posture management
- Executive summaries on security investigations
How Does Microsoft Security Copilot Work?
You can access Microsoft Security Copilot capabilities through a standalone experience. As well as embedded experiences available in other Microsoft security products.
Copilot integrates with several tools, including:
- Microsoft Sentinel
- Microsoft Defender XDR
- Microsoft Intune
- Microsoft Defender Threat Intelligence
- Microsoft Entra
- Microsoft Purview
- Microsoft Defender External Attack Surface Management
- Microsoft Defender for Cloud
You can use natural language prompts with Security Copilot. This makes it easy to ask for information or guidance on various security topics.
For example, you can ask:
- What are the best practices for securing Azure workloads?
- What is the impact of CVE-2024-23905 on my organization?
- Generate a report on the latest attack campaign.
- How do I remediate an incident involving TrickBot malware?
Image source: Microsoft Should You Use Microsoft Security Copilot?
The Pros:
- Advanced Threat Detection
Microsoft Security Copilot employs advanced algorithms. These detect and analyze threats that may go unnoticed by traditional security measures. It has the ability to adapt to new threats in real time. This enhances the security posture for organizations.
- Operational Efficiency
Copilot automates threat analysis. This allows security teams to focus on strategic decision-making. It also reduces the time and effort spent on manual data analysis. The tool streamlines workflows, enabling quicker responses to potential threats.
- Integration with Microsoft Products
Microsoft Security Copilot seamlessly integrates with several Microsoft products. This creates a comprehensive cybersecurity ecosystem. The synergy between these tools enhances threat visibility as well as response capabilities.
- Continuous Learning
The AI and machine learning components of Copilot continuously learn from new data. This improves their ability to identify and mitigate emerging threats over time. This adaptive learning approach ensures that the tool evolves. Which is important to do alongside the ever-changing threat landscape.
- Reduced False Positives
Copilot’s advanced algorithms contribute to a more accurate threat detection process. This minimizes false positives that can overwhelm security teams. The result is a more focused and efficient response to genuine threats.
The Considerations:
- Integration Challenges
Microsoft Security Copilot seamlessly integrates with Microsoft and other security products. But organizations using a diverse range of cybersecurity tools may face integration challenges. Consider the compatibility of Copilot with your existing cybersecurity infrastructure.
- Resource Requirements
The deployment of advanced AI and machine learning technologies may demand extra resources. Companies should check if their existing infrastructure supports the requirements of the tool.
- Training and Familiarization
Successfully leveraging the benefits of Copilot requires training. As well as familiarization with the tool’s functionalities. Ensure that your security team is adequately trained. This will maximize the potential of this cybersecurity solution.
The Bottom Line
Microsoft Security Copilot represents a leap forward in the realm of AI-driven cybersecurity. It has an advanced capacity for real-time threat detection and operational efficiency. As well as extensive integration capabilities. These factors make it a compelling choice. Especially for businesses seeking to fortify their
digital defenses.Your unique business needs should guide the decision to adopt Microsoft Security Copilot. Consider factors such as existing cybersecurity infrastructure and resource availability. As well as the commitment to ongoing training.
Get Expert Microsoft Product Support Here!
Microsoft is a vast ecosystem of interconnected business tools. Security Copilot is one of the newest to help you secure your online landscape. If you need some help leveraging these tools for your company, let us know. We are experienced Microsoft service providers. Our team can help you make the most of these tools.
Contact us today to schedule a consultation.
This Article has been Republished with Permission from The Technology Press.
- Smart Tactics to Reduce Cloud Waste at Your Business
Cloud computing has revolutionized the way businesses operate. It offers scalability, flexibility, and cost-efficiency. But cloud services also come with a downside: cloud waste.
Cloud waste is the unnecessary spending of resources and money on cloud services. These services are often not fully utilized or optimized. About 32% of cloud spending is wasted. This can lead to budget concerns as spending
skyrockets.But that figure also holds opportunity. It means that you can reduce nearly a third of cloud spending by optimizing how you use cloud tools.
So, how can you reduce cloud waste at your business and save money? Here are some smart tactics to consider.
Conduct a Comprehensive Cloud Audit
Before implementing any cost-cutting strategies, conduct an audit. It’s essential to have a clear understanding of your current cloud usage. Conducting a comprehensive cloud audit allows you to identify:
- Underutilized resources
- Overprovisioned instances
- Unnecessary services
Use cloud management tools to generate reports. Look at usage patterns, costs, and performance metrics. This initial assessment forms the foundation for implementing effective waste reduction tactics.
Put in Place Right-Sizing Strategies
Right-sizing involves matching your cloud resources to the actual demands of your workloads. Many businesses fall into the trap of overprovisioning. This means securing more user licenses or features than they need. This leads to increased costs and unnecessary waste.
Analyze your workload requirements and resize instances accordingly. Use tools provided by your cloud service provider. These tools can identify and adjust the capacity of instances. This ensures that you only pay for the resources you truly need.
Use Reserved Instances and Savings Plans
Cloud providers offer cost-saving options like Reserved Instances (RIs) and Savings Plans. These allow businesses to commit to a specific amount of usage. This is in exchange for discounted rates. By leveraging these options, you can significantly reduce your cloud costs over time.
Carefully analyze your workload and usage patterns. Then, determine the most cost-effective reserved capacity or savings plan. Find a plan that aligns with your business’s long-term goals.
Install Automated Scaling Policies
Dynamic workloads have a need for dynamic resource allocation. Install automated scaling policies. These ensure that your infrastructure scales up or down based on demand. This optimizes performance. It also prevents overprovisioning during periods of low activity.
Cloud services enable you to set predefined policies for scaling. Examples are AWS Auto Scaling and Autoscale in Azure. These features help ensure efficient resource utilization without manual intervention.
Track and Optimize Storage
Storage costs can accumulate quickly. This is especially true when data is not regularly reviewed and archived. Estimate your storage needs. Then, put in place lifecycle policies to automatically downsize lesser-used data such as transitioning less frequently accessed data to lower-cost storage options.
Regularly review and delete unnecessary data to free up storage space. Adopt a proactive approach to storage management. This can help you significantly reduce costs associated with data storage.
Schedule Your Cloud Resources
Schedule your cloud resources to run only when you need them. For example, turn off development, testing, or staging environments during nights and weekends. Or scale down your production environment during off-peak hours.
Use available tools to automate the scheduling of your cloud resources. Base this on automated rules and policies that you define.
Delete Unused or Orphaned Cloud Resources
Sometimes, you may forget or neglect to delete cloud resources. Resources that you no longer need or use. This can include:
- Snapshots
- Backups
- Volumes
- Load balancers
- IP addresses
- Unused accounts
These resources can accumulate over time and incur unnecessary costs. To avoid this, you should regularly audit your cloud environment. Delete any unused or orphaned resources your business is not using. You can often use cloud provider tools to find and remove these.
Weed Out Duplicate Services
Different departments in the same organization may be using duplicate services. Marketing may use one task management app, while Sales uses a different one. Centralize cloud resources and remove duplicate tools.
Having everyone use the same cloud tool for the same function can save money as well as enhance collaboration, reporting, and data integration.
Embrace Serverless Architecture
Serverless computing allows businesses to run applications without managing the underlying infrastructure. You pay only for the actual compute resources used for your processes. This eliminates the need for provisioning and maintaining servers. Which reduces both operational complexity and costs. Consider migrating suitable workloads to a serverless model. This can help you optimize resource use and cut cloud waste.
Schedule a Cloud Optimization Assessment Today!
By following these smart tactics, you can reduce cloud waste at your business as well as optimize your cloud spending. This helps you save money. You can also improve operational efficiency and environmental sustainability.
Are you struggling with expanding cloud costs? Need help identifying and removing cloud waste? Our team of cloud experts can help you.
Contact us today to schedule your assessment.
This Article has been Republished with Permission from The Technology Press.
- Eye-opening Insights from the 2023 Annual Cybersecurity Attitudes and Behaviors Report
We are living in an era dominated by digital connectivity. You can’t overstate the importance of cybersecurity. As technology advances, so do the threats that lurk in the online world.
Often, it’s our own actions that leave us most at risk of a cyberattack or online scam. Risky behaviors include weak passwords and lax security policies. As well as thinking “This won’t happen to me.” This is why human error is the cause of approximately 88% of data breaches.
The National Cybersecurity Alliance and CybSafe are working to correct poor cyber hygiene. Each year, the duo publishes a report on cybersecurity attitudes and behaviors. The goal is to educate both people and businesses. To educate them on how to better secure their digital landscapes.
This year’s study surveyed over 6,000 people across the U.S., Canada, the U.K., Germany, France, and New Zealand. The survey asked about several things. These include knowledge of cybersecurity risks, security best practices, and challenges faced.
The report reveals some eye-opening insights. These include how people perceive and respond to cyber threats. As well as what they can do to improve their cybersecurity posture. Here are some of the key findings from the report.
We Are Online… a Lot
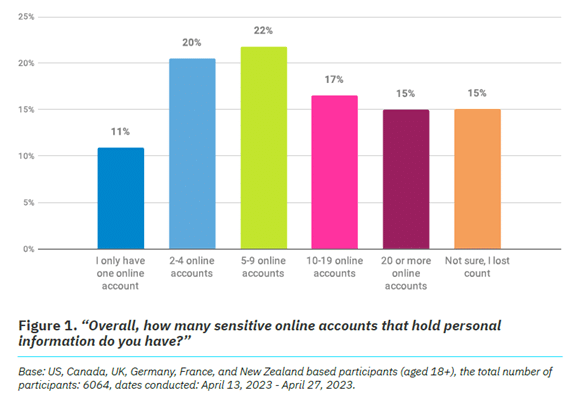
It’s no surprise that 93% of the study participants are online daily. The logins we create continue to expand, as well as those considered “sensitive.” Sensitive accounts hold personal information that could be harmful if stolen.
Nearly half (47%) of the study’s respondents have ten or more sensitive online accounts. This amplifies risk. Especially if people are using the same password for two or more of those accounts.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 Online Security Makes People Frustrated
Most people (84%) feel that online security is a priority. But as many as 39% feel frustrated, and nearly the same amount intimidated. It can seem that you just can’t get ahead of the hackers. Just over half of people thought digital security was under their control. That leaves a whole lot that don’t think so.
But that is no reason to let down your defenses and become an easy target. There are best practices you can put in place to safeguard your online accounts that work.
These include:
- Enabling multi-factor authentication on your accounts
- Using an email spam filter to catch phishing emails
- Adding a DNS filter to block malicious websites
- Using strong password best practices
People Need More Access to Cybersecurity Training
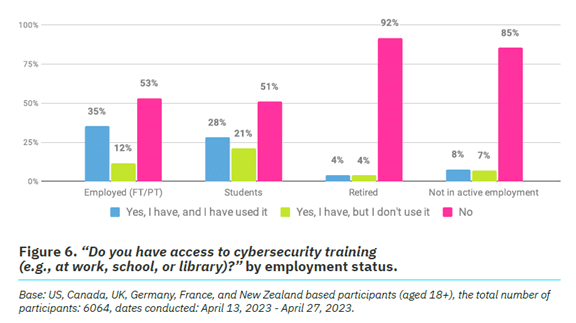
One way to reduce human errors associated with cybersecurity is to train people. The survey found that just 26% of respondents had access to cybersecurity training.
It also broke this down by employment status. We see that those not actively employed are most lacking. Even those employed can use more training access and encouragement. Just 53% report having access to cybersecurity awareness training and using it.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 Employers can significantly reduce their risk of falling victim to a data breach. They can do this by beefing up their security awareness training. There is also a large opportunity to provide more training. Particularly to those retired or not actively employed.
Cybercrime Reporting Is Increasing
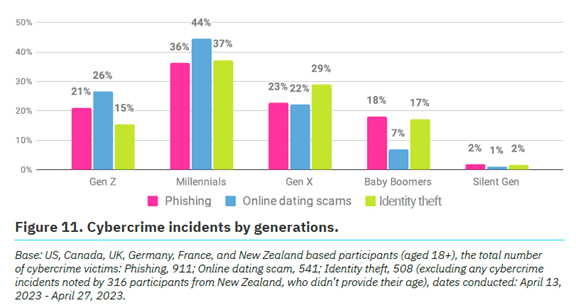
Over a quarter (27%) of survey participants said they had been a victim of cybercrime.
The types of cybercrimes reported include:
- Phishing (47%)
- Online dating scams (27%)
- Identity theft (26%)
Which generation reported the most cybercrime incidents? Millennials. In fact, Baby Boomers and the Silent Generation reported the fewest.
Source: The Annual Cybersecurity Attitudes and Behaviors Report 2023 No matter where you fall in the generations, it’s important to adopt security best
practices. We’ll go through some of these next.Online Security Best Practices to Reduce Your Risk
- Strong, Unique Passwords:
- Start with the basics. Create strong, unique passwords for each online account.
- Use a combination of uppercase and lowercase letters, numbers, and special characters.
- Multi-Factor Authentication (MFA):
- Enhance your account security with multi-factor authentication.
- MFA adds an extra barrier to unauthorized access. Even for
compromised passwords.
- Regular Software Updates:
- Keep all your software, including operating systems and mobile
apps, up to date.
- Keep all your software, including operating systems and mobile
- Beware of Phishing Attacks:
- Exercise caution when clicking on links or opening attachments
especially in emails from unknown sources. - Verify the legitimacy of emails and websites. Check for subtle
signs, such as misspelled URLs or unfamiliar sender addresses.
- Exercise caution when clicking on links or opening attachments
- Use Secure Wi-Fi Networks:
- Ensure you connect to a secure and password-protected Wi-Fi
network. - Avoid using public Wi-Fi for sensitive transactions. Unless using a virtual private network (VPN).
- Ensure you connect to a secure and password-protected Wi-Fi
- Data Backup:
- Regularly back up important data to an external device or a secure
cloud service.
- Regularly back up important data to an external device or a secure
- Use Antivirus and Anti-Malware Software:
- Install reputable antivirus and anti-malware software on all devices.
- Regularly scan your systems for potential threats.
- Be Mindful of Social Media Settings:
- Review and adjust your privacy settings on social media platforms.
- Limit the amount of personal information visible to the public.
- Secure Your Personal Devices:
- Lock your devices with strong passwords or biometric
authentication.
- Lock your devices with strong passwords or biometric
- Educate and Stay Informed:
- Educate yourself and your team through cybersecurity awareness
programs. This fosters a culture of vigilance and preparedness.
- Educate yourself and your team through cybersecurity awareness
Schedule Cybersecurity Awareness Training Today
A little education on cybersecurity goes a long way toward protecting your data. Our experts can provide security training at the level you need. We’ll help you fortify your defenses against phishing, scams, and cyberattacks.
Contact us today to schedule a chat.
This Article has been Republished with Permission from The Technology Press.